Every machine needs a name. As soon as the second server is ready to go, the name SERVER no longer seems like a great idea. When deciding how to name servers, there are two primary conventions: functional names and unique names.
Functional Names
Functional names take the job assigned to …
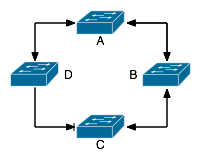 In this simple network of …
In this simple network of …